Turn AI into an individual execution system, Claude's latest Managed Agents Best Practices Guide
Original Article Title: Launching Claude Managed Agents
Original Author: Lance Martin
Translation: Peggy, BlockBeats
Editor's Note: This article introduces the Managed Agents launched by Claude. It provides a software form closer to the future: intelligent agents are no longer interfaces that respond to requests once but are execution systems that can be configured, deployed, scheduled, and run for the long term.
By thoroughly decoupling "intelligence" (model and runtime framework), "execution" (tools and sandbox), and "process" (session and log), Claude Managed Agents transform the agent from "logic in code" to an independent infrastructure unit. This design not only enhances the system's stability and security in long-running tasks but also allows agents to continuously expand as the model's capabilities evolve, unconstrained by existing frameworks.
Within this framework, common usage patterns have also changed: from event-triggered and scheduled execution to "trigger-on-delivery" automatic execution, and to complex tasks spanning days or even weeks, agents truly acquire the ability to "work continuously." This means that the value of AI is no longer only reflected in the quality of a single answer but in its ability to accumulate and compound over time.
If past APIs allowed developers to "invoke intelligence," Managed Agents are now attempting to answer another question: how to make intelligence a system that can be hosted, scheduled, and run continuously. In this sense, agents are no longer just tools but closer to a new computing primitive.
The original article is as follows:
TL;DR
Claude Managed Agents are a pre-built, configurable agent execution framework (agent harness) that runs on managed infrastructure. You only need to define an agent as a template—including tools, skills, file/code repositories, etc.—and the rest of the runtime framework and infrastructure are provided by the system. This system is designed to keep pace with Claude's rapidly growing intelligence levels and support long-running tasks.
Related links:
·Claude Blog: Patterns of use and customer cases
·Engineering Blog: Design of Claude Managed Agents
·Documentation: Getting Started Guide, Quick Start, CLI and SDK Overview
Claude Managed Agents
Why Claude Managed Agents are Needed
Claude's messages API is fundamentally an entry point to interact directly with the model: input a message, get back a content block. Intelligent agents built on the messages API need to rely on a "runtime framework" to handle tool invocation routing, context management, and more. However, this poses several challenges:
1. The runtime framework needs to keep up with Claude's evolving capabilities
I recently wrote a blog post on how to build an agent based on Claude API's underlying capabilities for handling tool orchestration and context management. However, the issue is that the agent's runtime framework often implies some assumptions about "what Claude cannot do." As Claude's capabilities grow, these assumptions quickly become outdated and may even become performance bottlenecks. Therefore, the runtime framework must be continually updated to keep pace with Claude's rate of evolution.
2. Claude's task lifecycles are becoming longer
The span of tasks that Claude can handle is growing exponentially, exceeding 10 hours of human work in METR benchmark tests. This places higher demands on the agent's underlying infrastructure: it must have security, stability in long-running scenarios (handling various infrastructure failures), and scalability (e.g., supporting multiple teams of agents running simultaneously).
Why These Challenges Matter
Addressing the challenges mentioned above is crucial because we anticipate that future versions of Claude will be able to operate continuously over periods of days, weeks, or even months, tackling humanity's most complex problems.
The Claude Agent SDK is the first step in this direction, providing a general-purpose, easy-to-use intelligent agent runtime framework. Meanwhile, Claude Managed Agents take it a step further: building on this foundation, they provide a complete runtime framework + managed infrastructure specifically designed to support secure, reliable task execution over long time spans.
Getting Started
A simple way to get started is by using our open-source claude-api skill, which can be used out of the box in Claude Code. Simply install the latest version of Claude Code, then run the following subcommand to complete the initialization configuration of Claude Managed Agents.
I personally have a strong preference for the "skills" approach to integrating new functionality, and I extensively use this skill in practice.
Additionally, you can refer to our documentation to quickly get started with the SDK or CLI and prototype your agents in the Claude Console.
Use Cases
You can find many interesting use cases in the Claude official blog. Combining these cases with my own practical experience, I have observed some common usage patterns:
1. Event-Triggered
Task execution by a Managed Agent triggered by a service.
For example, when a bug is detected in the system, an automated call to a managed agent is made to write a patch and submit a PR. No human intervention is required between the "issue identified" and "patch applied" stages.
2. Scheduled Execution
Scheduling tasks for a Managed Agent to execute.
For instance, many people, including myself, use this method to generate daily briefings (such as a summary of activities on Platform X or GitHub, or a team's progress report generated by an agent). Below is an example of my daily summary of activities on Platform X.

3. Fire-and-Forget
Task execution by a Managed Agent triggered by a human but requiring no ongoing follow-up. For instance, assigning tasks to a managed agent via Slack or Teams, which then autonomously completes the task and delivers the results (such as tables, slides, or even applications).
4. Long-horizon Tasks
A long-running task, which I consider one of the particularly valuable scenarios for Managed Agents.
I have conducted some experiments based on Andrej Karpathy's auto-research repo, exploring different ways of application. For example, I recently took _chenglou's pretext library as input and had a Managed Agent research how to apply it to our engineering blog content.
Core Concepts
There are three core concepts to understand in the onboarding process:
1. Agent
A version-controlled configuration that defines the "identity" of the agent: including the model, system prompt, tools, skills, MCP server, etc. Once created, it can be invoked repeatedly via ID.
2. Environment
A template used to describe the sandbox environment provided for the agent tool to run (e.g., runtime type, network policy, dependency package configuration, etc.).
3. Session
A stateful running instance launched based on a preconfigured agent and environment. It will create a brand-new sandbox from the environment template, mount the resources needed for this run (such as files, GitHub repositories), and securely store authentication information in a keystore (like MCP credentials).
You can think of it this way:
· Agent = The configuration itself
· Environment = The sandbox template required for agent operation
· Session = One specific execution process
One Agent can correspond to multiple Sessions.
Usage
Refer to the documentation for details. The overall usage is divided into two categories:
1. SDK (Code-Oriented)
Integrate the SDK into your application to drive sessions at runtime. Currently, Managed Agents support 6 languages: Python, TypeScript, Java, Go, Ruby, PHP.
2. CLI (Command Line Interface)
Interact with all API resources via the command line, including agents, environments, sessions, vaults, skills, files, etc. Each type of resource has corresponding subcommands.
Common Practice:
Usually, the CLI is used for configuration and initialization, while the SDK is used for runtime logic.
An agent template is persistent—you can create a template (e.g., defining the model, system prompt, tools, MCP server, skills in YAML), store it in Git, and apply it during the deployment process via the CLI.
Workflow
I co-authored an Anthropic engineering blog post with @mc_anthropic, @gcemaj, and @jkeatn, which provided a detailed explanation of the construction of Claude Managed Agents. A key conclusion in the article was that enabling agents to scale with Claude's intelligence level is fundamentally an "infrastructure problem," not just a runtime framework design issue.
This means that the real challenge lies not in "how to write a smarter agent," but in how to build a system that can run stably in the long term, be scalable, and be evolvable, allowing the agent to undertake increasingly complex and long-term tasks.
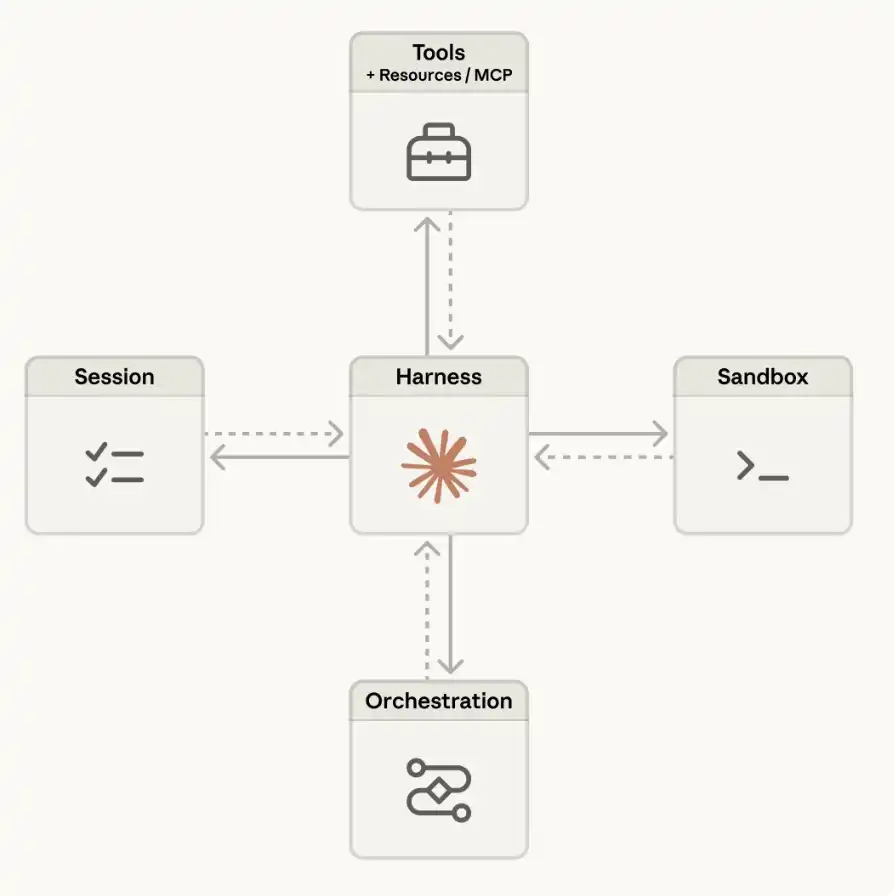
Based on this philosophy, we did not design a fixed agent runtime framework (harness) as we anticipated its continuous evolution. Instead, we "decoupled" several key parts of the system:
“Brain” (Claude and its runtime framework)
“Hands” (sandbox and tool performing concrete actions)
“Session” (records event logs of execution)
These three were designed as independent interfaces with minimal assumptions about each other. Each part can fail or be replaced independently without affecting the overall system.
In the article, we also shared how this architecture brings higher reliability, security, and flexibility—while also leaving room for future integration of new runtime frameworks, sandboxes, or infrastructure hosting sessions.
Conclusion
I am very excited about projects exploring Multi-Agent Orchestration or long-horizon tasks. One thing that has always frustrated me in the past is how the agent's execution framework struggles to keep up with the evolving capabilities of the model.
The significance of Claude Managed Agents is that it takes care of the execution framework and infrastructure layer for you, allowing you to focus on a higher level—treating the "agent" itself as a new foundational primitive in the Claude API, enabling further exploration and development on top of it.
You may also like

Stolen: $290 million, Three Parties Refusing to Acknowledge, Who Should Foot the Bill for the KelpDAO Incident Resolution?

ASTEROID Pumped 10,000x in Three Days, Is Meme Season Back on Ethereum?

ChainCatcher Hong Kong Themed Forum Highlights: Decoding the Growth Engine Under the Integration of Crypto Assets and Smart Economy

Why can this institution still grow by 150% when the scale of leading crypto VCs has shrunk significantly?

Anthropic's $1 trillion, compared to DeepSeek's $100 billion

Geopolitical Risk Persists, Is Bitcoin Becoming a Key Barometer?

Annualized 11.5%, Wall Street Buzzing: Is MicroStrategy's STRC Bitcoin's Savior or Destroyer?

An Obscure Open Source AI Tool Alerted on Kelp DAO's $292 million Bug 12 Days Ago

Mixin has launched USTD-margined perpetual contracts, bringing derivative trading into the chat scene.
The privacy-focused crypto wallet Mixin announced today the launch of its U-based perpetual contract (a derivative priced in USDT). Unlike traditional exchanges, Mixin has taken a new approach by "liberating" derivative trading from isolated matching engines and embedding it into the instant messaging environment.
Users can directly open positions within the app with leverage of up to 200x, while sharing positions, discussing strategies, and copy trading within private communities. Trading, social interaction, and asset management are integrated into the same interface.
Based on its non-custodial architecture, Mixin has eliminated friction from the traditional onboarding process, allowing users to participate in perpetual contract trading without identity verification.
The trading process has been streamlined into five steps:
· Choose the trading asset
· Select long or short
· Input position size and leverage
· Confirm order details
· Confirm and open the position
The interface provides real-time visualization of price, position, and profit and loss (PnL), allowing users to complete trades without switching between multiple modules.
Mixin has directly integrated social features into the derivative trading environment. Users can create private trading communities and interact around real-time positions:
· End-to-end encrypted private groups supporting up to 1024 members
· End-to-end encrypted voice communication
· One-click position sharing
· One-click trade copying
On the execution side, Mixin aggregates liquidity from multiple sources and accesses decentralized protocol and external market liquidity through a unified trading interface.
By combining social interaction with trade execution, Mixin enables users to collaborate, share, and execute trading strategies instantly within the same environment.
Mixin has also introduced a referral incentive system based on trading behavior:
· Users can join with an invite code
· Up to 60% of trading fees as referral rewards
· Incentive mechanism designed for long-term, sustainable earnings
This model aims to drive user-driven network expansion and organic growth.
Mixin's derivative transactions are built on top of its existing self-custody wallet infrastructure, with core features including:
· Separation of transaction account and asset storage
· User full control over assets
· Platform does not custody user funds
· Built-in privacy mechanisms to reduce data exposure
The system aims to strike a balance between transaction efficiency, asset security, and privacy protection.
Against the background of perpetual contracts becoming a mainstream trading tool, Mixin is exploring a different development direction by lowering barriers, enhancing social and privacy attributes.
The platform does not only view transactions as execution actions but positions them as a networked activity: transactions have social attributes, strategies can be shared, and relationships between individuals also become part of the financial system.
Mixin's design is based on a user-initiated, user-controlled model. The platform neither custodies assets nor executes transactions on behalf of users.
This model aligns with a statement issued by the U.S. Securities and Exchange Commission (SEC) on April 13, 2026, titled "Staff Statement on Whether Partial User Interface Used in Preparing Cryptocurrency Securities Transactions May Require Broker-Dealer Registration."
The statement indicates that, under the premise where transactions are entirely initiated and controlled by users, non-custodial service providers that offer neutral interfaces may not need to register as broker-dealers or exchanges.
Mixin is a decentralized, self-custodial privacy wallet designed to provide secure and efficient digital asset management services.
Its core capabilities include:
· Aggregation: integrating multi-chain assets and routing between different transaction paths to simplify user operations
· High liquidity access: connecting to various liquidity sources, including decentralized protocols and external markets
· Decentralization: achieving full user control over assets without relying on custodial intermediaries
· Privacy protection: safeguarding assets and data through MPC, CryptoNote, and end-to-end encrypted communication
Mixin has been in operation for over 8 years, supporting over 40 blockchains and more than 10,000 assets, with a global user base exceeding 10 million and an on-chain self-custodied asset scale of over $1 billion.

$600 million stolen in 20 days, ushering in the era of AI hackers in the crypto world

Vitalik's 2026 Hong Kong Web3 Summit Speech: Ethereum's Ultimate Vision as the "World Computer" and Future Roadmap

On the same day Aave introduced rsETH, why did Spark decide to exit?

Full Post-Mortem of the KelpDAO Incident: Why Did Aave, Which Was Not Compromised, End Up in Crisis Situation?

After a $290 million DeFi liquidation, is the security promise still there?

ZachXBT's post ignites RAVE nearing zero, what is the truth behind the insider control?

Vitalik 2026 Hong Kong Web3 Carnival Speech Transcript: We do not compete on speed; security and decentralization are the core

In-depth Analysis of RAVE Events: Short Squeeze, Crash, and Quantitative Financial Models of Liquidity Manipulation











