Loss Exceeds $1 Million, Fake Zoom Meeting Phishing Analysis
Original Title: "Seeing is Not Believing | Analysis of Fake Zoom Meeting Phishing"
Original Source: SlowMist Technology
Background
Recently, several users on platform X reported a phishing attack method that disguised itself as a Zoom meeting link. One victim clicked on a malicious Zoom meeting link, which led to the installation of malware, resulting in the theft of encrypted assets and losses amounting to millions of dollars. In this context, the SlowMist security team conducted an analysis of this phishing event and attack method, and traced the hacker's fund flow.
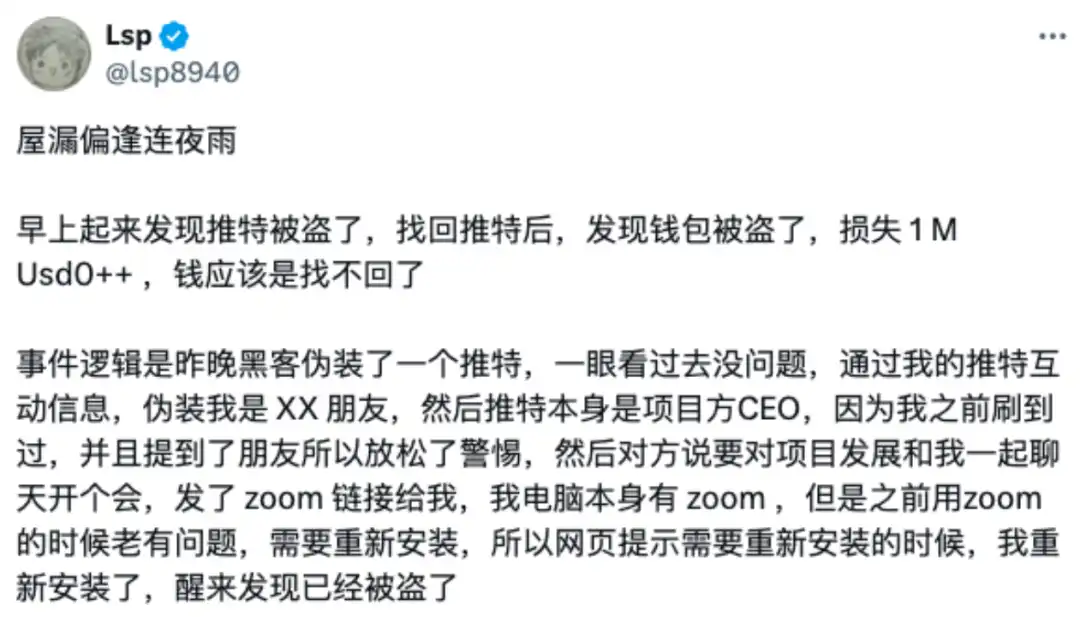
(https://x.com/lsp8940/status/1871350801270296709)
Phishing Link Analysis
The hacker used a domain name like "app[.]us4zoom[.]us" to disguise itself as a legitimate Zoom meeting link. The page closely resembled a real Zoom meeting, and when users clicked the "Start Meeting" button, it triggered the download of a malicious installer package instead of starting the local Zoom client.

Through probing the above domain, we discovered the hacker's monitoring log address (https[:]//app[.]us4zoom[.]us/error_log).

Upon decryption, it was found that this was a log entry when the script attempted to send a message via the Telegram API, using the Russian language.

The site was deployed online 27 days ago, and the hacker may be Russian. Since November 14th, they have been seeking targets and then monitoring through the Telegram API to see if any targets click the download button on the phishing page.

Malware Analysis
The malicious installer package's filename is "ZoomApp_v.3.14.dmg." Below is the interface opened by this Zoom phishing software, which prompts users to execute the ZoomApp.file malicious script in Terminal and also prompts users to enter their local password during the execution process.

Below is the execution content of this malicious file:

Upon decoding the above content, it was found to be a malicious osascript script.

Further analysis revealed that the script searches for a hidden executable file named ".ZoomApp" and runs it locally. We conducted disk analysis on the original installation package "ZoomApp_v.3.14.dmg" and indeed found that the package was hiding an executable file named ".ZoomApp".

Malicious Behavior Analysis
Static Analysis
We uploaded this binary file to a threat intelligence platform for analysis, and the file was identified as malicious.

(https://www.virustotal.com/gui/file/e4b6285e183dd5e1c4e9eaf30cec886fd15293205e706855a48b30c890cbf5f2)
Through static disassembly analysis, the following is the entry code of this binary file, used for data decryption and script execution.

Below is the data section, where it can be observed that most of the information has been encrypted and encoded.

Upon decrypting the data, it was found that this binary file ultimately executes a malicious osascript script (complete decryption code shared at: https://pastebin.com/qRYQ44xa), which collects information from the user's device and sends it to a backend.
Below is a section of the code enumerating different plugin ID paths.

Below is a section of the code reading KeyChain information from the computer.

The malicious code, after collecting system information, browser data, encrypted wallet data, Telegram data, Notes data, and Cookie data, compresses them and sends them to a hacker-controlled server (141.98.9.20).

Since the malware prompts users to enter their password during runtime and subsequent malicious scripts also collect KeyChain data from the computer (potentially containing various passwords saved by the user on the computer), the hacker, upon collection, will attempt to decrypt the data to obtain sensitive information such as the user's wallet mnemonic phrase and private key, thereby stealing the user's assets.
Analysis shows that the IP address of the hacker's server is located in the Netherlands and has been flagged as malicious by a threat intelligence platform.

(https://www.virustotal.com/gui/ip-address/141.98.9.20)
Dynamic Analysis
By dynamically executing this malicious program in a virtual environment and analyzing the process, the following image shows the process monitoring information of the malicious program collecting local data and sending data to the backend.


MistTrack Analysis
We used the on-chain tracking tool MistTrack to analyze the hacker address provided by the victim: 0x9fd15727f43ebffd0af6fecf6e01a810348ee6ac. The hacker address has profited over $1 million, including USD0++, MORPHO, and ETH; of which, USD0++ and MORPHO were exchanged for 296 ETH.
According to MistTrack, the hacker address has received small amounts of ETH from address 0xb01caea8c6c47bbf4f4b4c5080ca642043359c2e, presumably as a fee for the hacker address. The address (0xb01c) only has one source of income but has sent out small amounts of ETH to nearly 8,800 addresses, appearing to be a "platform specifically providing fees."

Filter out the outgoing addresses from this address (0xb01c) that have been flagged as malicious, associated with two phishing addresses, one of which is marked as the Pink Drainer, and further analyze these two phishing addresses, with funds mostly transferred to ChangeNOW and MEXC.

Next, analyze the outgoing transactions of the stolen funds, where a total of 296.45 ETH was transferred to a new address 0xdfe7c22a382600dcffdde2c51aaa73d788ebae95.

The first transaction from the new address (0xdfe7) was in July 2023, involving multiple chains, and the current balance is 32.81 ETH.

The main ETH outflow paths from the new address (0xdfe7) are as follows:
· 200.79 ETH -> 0x19e0…5c98f
· 63.03 ETH -> 0x41a2…9c0b
· 8.44 ETH -> Exchanged for 15,720 USDT
· 14.39 ETH -> Gate.io

The subsequent outflows from the expanded addresses are associated with multiple platforms such as Bybit, Cryptomus.com, Swapspace, Gate.io, MEXC, and are related to multiple addresses marked by MistTrack as Angel Drainer and Theft. Additionally, there is currently 99.96 ETH remaining in the address 0x3624169dfeeead9f3234c0ccd38c3b97cecafd01.

The USDT transaction trace from the new address (0xdfe7) is also extensive, with transfers to platforms such as Binance, MEXC, FixedFloat, and others.

Summary
The phishing method shared this time is where hackers disguise themselves as a legitimate Zoom meeting link, tricking users into downloading and executing malicious software. This malware usually has multiple harmful functions such as collecting system information, stealing browser data, and obtaining cryptocurrency wallet information, which is then transmitted to a server controlled by the hacker. These types of attacks often combine social engineering and trojan horse attack techniques, making users vulnerable to falling victim with slight carelessness. The SlowMist Security Team advises users to carefully verify before clicking on any meeting links, avoid executing software and commands from unknown sources, install antivirus software, and keep it updated regularly. For more security insights, it is recommended to read the SlowMist Security Team's "Blockchain Dark Forest Self-Rescue Handbook": https://github.com/slowmist/Blockchain-dark-forest-selfguard-handbook/blob/main/README_CN.md.
You may also like

Consumer-grade Crypto Global Survey: Users, Revenue, and Track Distribution

Prediction Markets Under Bias

Stolen: $290 million, Three Parties Refusing to Acknowledge, Who Should Foot the Bill for the KelpDAO Incident Resolution?

ASTEROID Pumped 10,000x in Three Days, Is Meme Season Back on Ethereum?

ChainCatcher Hong Kong Themed Forum Highlights: Decoding the Growth Engine Under the Integration of Crypto Assets and Smart Economy

Why can this institution still grow by 150% when the scale of leading crypto VCs has shrunk significantly?

Anthropic's $1 trillion, compared to DeepSeek's $100 billion

Geopolitical Risk Persists, Is Bitcoin Becoming a Key Barometer?

Annualized 11.5%, Wall Street Buzzing: Is MicroStrategy's STRC Bitcoin's Savior or Destroyer?

An Obscure Open Source AI Tool Alerted on Kelp DAO's $292 million Bug 12 Days Ago

Mixin has launched USTD-margined perpetual contracts, bringing derivative trading into the chat scene.
The privacy-focused crypto wallet Mixin announced today the launch of its U-based perpetual contract (a derivative priced in USDT). Unlike traditional exchanges, Mixin has taken a new approach by "liberating" derivative trading from isolated matching engines and embedding it into the instant messaging environment.
Users can directly open positions within the app with leverage of up to 200x, while sharing positions, discussing strategies, and copy trading within private communities. Trading, social interaction, and asset management are integrated into the same interface.
Based on its non-custodial architecture, Mixin has eliminated friction from the traditional onboarding process, allowing users to participate in perpetual contract trading without identity verification.
The trading process has been streamlined into five steps:
· Choose the trading asset
· Select long or short
· Input position size and leverage
· Confirm order details
· Confirm and open the position
The interface provides real-time visualization of price, position, and profit and loss (PnL), allowing users to complete trades without switching between multiple modules.
Mixin has directly integrated social features into the derivative trading environment. Users can create private trading communities and interact around real-time positions:
· End-to-end encrypted private groups supporting up to 1024 members
· End-to-end encrypted voice communication
· One-click position sharing
· One-click trade copying
On the execution side, Mixin aggregates liquidity from multiple sources and accesses decentralized protocol and external market liquidity through a unified trading interface.
By combining social interaction with trade execution, Mixin enables users to collaborate, share, and execute trading strategies instantly within the same environment.
Mixin has also introduced a referral incentive system based on trading behavior:
· Users can join with an invite code
· Up to 60% of trading fees as referral rewards
· Incentive mechanism designed for long-term, sustainable earnings
This model aims to drive user-driven network expansion and organic growth.
Mixin's derivative transactions are built on top of its existing self-custody wallet infrastructure, with core features including:
· Separation of transaction account and asset storage
· User full control over assets
· Platform does not custody user funds
· Built-in privacy mechanisms to reduce data exposure
The system aims to strike a balance between transaction efficiency, asset security, and privacy protection.
Against the background of perpetual contracts becoming a mainstream trading tool, Mixin is exploring a different development direction by lowering barriers, enhancing social and privacy attributes.
The platform does not only view transactions as execution actions but positions them as a networked activity: transactions have social attributes, strategies can be shared, and relationships between individuals also become part of the financial system.
Mixin's design is based on a user-initiated, user-controlled model. The platform neither custodies assets nor executes transactions on behalf of users.
This model aligns with a statement issued by the U.S. Securities and Exchange Commission (SEC) on April 13, 2026, titled "Staff Statement on Whether Partial User Interface Used in Preparing Cryptocurrency Securities Transactions May Require Broker-Dealer Registration."
The statement indicates that, under the premise where transactions are entirely initiated and controlled by users, non-custodial service providers that offer neutral interfaces may not need to register as broker-dealers or exchanges.
Mixin is a decentralized, self-custodial privacy wallet designed to provide secure and efficient digital asset management services.
Its core capabilities include:
· Aggregation: integrating multi-chain assets and routing between different transaction paths to simplify user operations
· High liquidity access: connecting to various liquidity sources, including decentralized protocols and external markets
· Decentralization: achieving full user control over assets without relying on custodial intermediaries
· Privacy protection: safeguarding assets and data through MPC, CryptoNote, and end-to-end encrypted communication
Mixin has been in operation for over 8 years, supporting over 40 blockchains and more than 10,000 assets, with a global user base exceeding 10 million and an on-chain self-custodied asset scale of over $1 billion.

$600 million stolen in 20 days, ushering in the era of AI hackers in the crypto world

Vitalik's 2026 Hong Kong Web3 Summit Speech: Ethereum's Ultimate Vision as the "World Computer" and Future Roadmap

On the same day Aave introduced rsETH, why did Spark decide to exit?

Full Post-Mortem of the KelpDAO Incident: Why Did Aave, Which Was Not Compromised, End Up in Crisis Situation?

After a $290 million DeFi liquidation, is the security promise still there?

ZachXBT's post ignites RAVE nearing zero, what is the truth behind the insider control?



