Crypto Christmas Heist: Over $6 Million Lost, Trust Wallet Chrome Extension Wallet Hacked Analysis
Original Title: "Christmas Heist | Trust Wallet Browser Extension Wallet Hacked Analysis"
Original Source: SlowMist Technology
Background
Early this morning Beijing time, @zachxbt announced in the channel, "Some Trust Wallet users reported that funds in their wallet addresses have been stolen in the past few hours." Subsequently, Trust Wallet's official X also released an official statement confirming a security vulnerability in Trust Wallet Browser Extension version 2.68, advising all users using version 2.68 to immediately disable this version and upgrade to version 2.69.

Tactics
Upon receiving the intelligence, the SlowMist security team promptly conducted an analysis of the relevant samples. Let's first compare the core code of the previously released 2.67 and 2.68 versions:


By diffing the code of the two versions, we found the malicious code added by the hacker:

The malicious code will traverse all wallets in the plugin, make a "get mnemonic phrase" request for each user's wallet to obtain the user's encrypted mnemonic phrase, and finally use the password or passkeyPassword entered by the user when unlocking the wallet for decryption. If decryption is successful, the user's mnemonic phrase will be sent to the attacker's domain `api.metrics-trustwallet[.]com`.

We also analyzed the attacker's domain information; the attacker used the domain: metrics-trustwallet.com.

Upon investigation, the registration time of this malicious domain was 2025-12-08 02:28:18, and the domain registrar is: NICENIC INTERNATIONA.
Request records targeting api.metrics-trustwallet[.]com began on 2025-12-21.

This timestamp and the implantation of the backdoor with code 12.22 are roughly the same.
We continue to reproduce the entire attack process through code tracking analysis:
Through dynamic analysis, it can be seen that after unlocking the wallet, the attacker filled the mnemonic information into the error in R1.

And the source of this Error data is obtained through the GET_SEED_PHRASE function call. Currently, Trust Wallet supports two ways to unlock: password and passkeyPassword. The attacker, during the unlocking process, obtained the password or passkeyPassword, then called GET_SEED_PHRASE to obtain the wallet's mnemonic phrase (private key as well), and then placed the mnemonic phrase in the "errorMessage".

Below is the code using emit to call GetSeedPhrase to obtain the mnemonic phrase data and fill it into the error.

Traffic analysis performed through BurpSuite shows that after obtaining the mnemonic phrase, it is encapsulated in the request body's errorMessage field and sent to a malicious server (https[://]api[.]metrics-trustwallet[.]com), which is consistent with the previous analysis.

Through the above process, the theft of the mnemonic phrase/private key is completed. In addition, the attacker is also familiar with the source code and utilizes the open-source full-lifecycle product analysis platform PostHogJS to collect user wallet information.
Stolen Asset Analysis

(https://t.me/investigations/296)
According to ZachXBT's disclosed hacker address, we have calculated that as of the time of publication, the total amount of stolen assets on the Bitcoin blockchain is approximately 33 BTC (valued at around 3 million USD), the stolen assets on the Solana blockchain are valued at around 431 USD, and the stolen assets on the Ethereum mainnet and Layer 2 chains are valued at around 3 million USD. After stealing the coins, the hacker used various centralized exchanges and cross-chain bridges to transfer and exchange some of the assets.


Summary
This backdoor incident originated from a malicious code modification to the Trust Wallet extension's internal codebase (analytics service logic), rather than the introduction of a tampered third-party package (such as a malicious npm package). The attacker directly altered the application's own code, using the legitimate PostHog library to redirect analytics data to a malicious server. Therefore, we have reason to believe this was a professional APT attack, where the attacker may have gained control of Trust Wallet-related developers' device or release deployment permissions prior to December 8.
Recommendations:
1. If you have installed the Trust Wallet extension wallet, you should immediately disconnect from the internet as a prerequisite for investigation and actions.
2. Immediately export your private key/mnemonic phrase and uninstall the Trust Wallet extension wallet.
3. After backing up your private key/mnemonic phrase, promptly transfer your funds to another wallet.
You may also like
X Pulls the Plug — the Era of “Talking Your Way to Traffic” Comes to an End.
Other people’s traffic will always belong to them—not to you.

First Zero, First Revival: A Real Story from the WEEX Global AI Trading Hackathon Preliminary Round
WEEX Labs, the innovation arm of the global crypto exchange WEEX, launched the preliminary round of its flagship AI trading hackathon, AI Wars: WEEX Alpha Awakens, on January 12, 2026. Backed by world-class sponsors including AWS, the prize pool has reached $1.88 million, with a Bentley Bentayga S awaiting the champion in Dubai. Already, 788 elite teams worldwide are battling for a spot in the finals. This is more than a hackathon — it is a real-market stress test for AI trading. Registration remains open until January 18. If you want your AI to face real volatility, this is your moment.
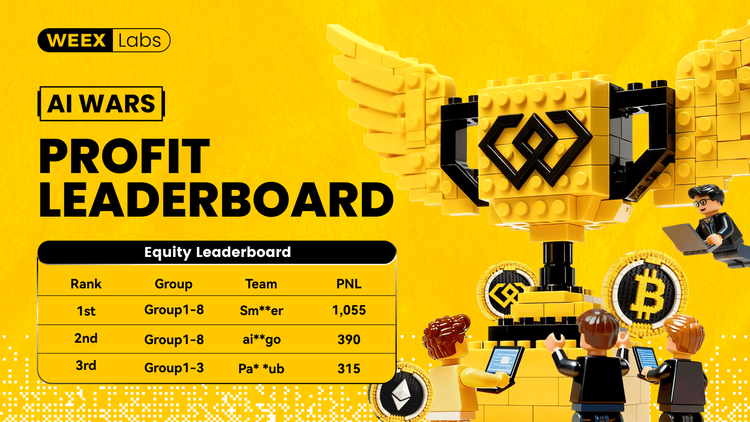
AI Wars: WEEX Alpha Awakens – Insights, Top Strategies, and Real-Market Execution Takeaways
WEEX Labs has officially launched the preliminary round of its global AI trading hackathon, AI Wars: WEEX Alpha Awakens, bringing together hundreds of elite teams to compete in real-market conditions. With a record-breaking $1.88 million prize pool and backing from top-tier sponsors like AWS, the event has quickly become a global proving ground for AI-powered trading strategies. As competition intensifies and standout teams emerge on the leaderboard, the hackathon not only showcases cutting-edge AI execution and risk management, but also offers valuable insights and inspiration for traders looking to build or refine their own AI-driven systems.

WEEX P2P now supports Polish zloty (PLN)—new users and merchant rewards
To make crypto deposits easier, WEEX has officially launched its P2P trading platform and continues to expand fiat support. We're excited to announce that the Polish Zloty (PLN) is now available on WEEX P2P!

Layoffs of 30%, But Spending $250 Million to Buy a Company - What Is Polygon Thinking?

Sentient Reveals Tokenomics, How Will the Market Price It?

AI in the Crypto Market: How Artificial Intelligence is Changing Trading Strategies
This article explores how AI contributes to these movements and share practical strategies to help you navigate an AI-powered crypto market.

Yen Weakness Nears Inflation Red Line: Bank of Japan May Be Forced to Hike Early

Cross-chain Collaboration: Tom Lee Invests $200 Million, Joins Forces with Global Top Streamer Mr. Beast

Interactive Brokers Integrates USDC, US Bank Questions Stablecoin, What's the Overseas Buzz?

Trump Waves Hand, Stirs Venezuela's Game Hurricane

The Genius Stopping Law: Why Did Coinbase Backpedal at the Eleventh Hour?

Fact Check: How Much Money Did the University of Chicago Lose in its Crypto Investment?

Rumor has it that Coinbase is set to acquire Farcaster, still an Acquihire.

VanEck Q1 Market Outlook: Long-Term Bullish on Cryptocurrency, Strong Gold Demand

In the span of a week, what does Twitter's continuous updating on the Coin Circle Plate reform and Musk's intentions mean?

By seizing the first five seconds of Gold Dog, "Dry Sitting P Junior" earns $430,000 in 30 days.

DAU of 8? The Data Truth in the Solana vs. Starknet Public Opinion Battle
X Pulls the Plug — the Era of “Talking Your Way to Traffic” Comes to an End.
Other people’s traffic will always belong to them—not to you.
First Zero, First Revival: A Real Story from the WEEX Global AI Trading Hackathon Preliminary Round
WEEX Labs, the innovation arm of the global crypto exchange WEEX, launched the preliminary round of its flagship AI trading hackathon, AI Wars: WEEX Alpha Awakens, on January 12, 2026. Backed by world-class sponsors including AWS, the prize pool has reached $1.88 million, with a Bentley Bentayga S awaiting the champion in Dubai. Already, 788 elite teams worldwide are battling for a spot in the finals. This is more than a hackathon — it is a real-market stress test for AI trading. Registration remains open until January 18. If you want your AI to face real volatility, this is your moment.
AI Wars: WEEX Alpha Awakens – Insights, Top Strategies, and Real-Market Execution Takeaways
WEEX Labs has officially launched the preliminary round of its global AI trading hackathon, AI Wars: WEEX Alpha Awakens, bringing together hundreds of elite teams to compete in real-market conditions. With a record-breaking $1.88 million prize pool and backing from top-tier sponsors like AWS, the event has quickly become a global proving ground for AI-powered trading strategies. As competition intensifies and standout teams emerge on the leaderboard, the hackathon not only showcases cutting-edge AI execution and risk management, but also offers valuable insights and inspiration for traders looking to build or refine their own AI-driven systems.
WEEX P2P now supports Polish zloty (PLN)—new users and merchant rewards
To make crypto deposits easier, WEEX has officially launched its P2P trading platform and continues to expand fiat support. We're excited to announce that the Polish Zloty (PLN) is now available on WEEX P2P!
